Security-Enhanced Linux (SELinux) is a Linux kernel security module. It provides policies for mandatory access controls (MAC). Although we do not recommend that you permanently disable SELinux, it is sometimes necessary to troubleshoot issues on a system.
In this Linux quick tip we will explain how to check the current status of SELinux. We will also discuss how to temporarily disable SELinux, as well as permanently disable it.
Check Current Status of SELinux
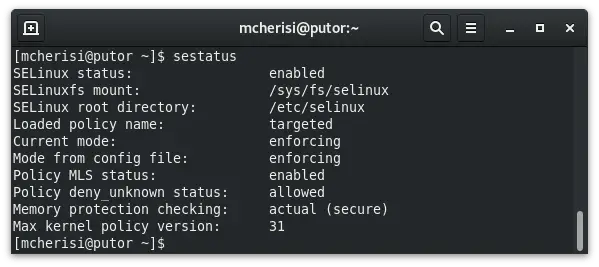
You can check the current status of SELinux using the sestatus command. This will show you whether it’s enabled or disable, the current mode, and the mode set in the config file in addition to other information.
You can also quickly get the current running mode with the getenforce command.
[mcherisi@putor ~]$ getenforce
EnforcingTemporarily Disable SELinux
If you are troubleshooting issues, or need to check if SELinux is causing something to fail, you can temporarily disable SELinux. There is a set of commands to easily achieve this. In the section above, we spoke about using the getenforce command to get the current mode. You can use the setenforce command to set the current mode.
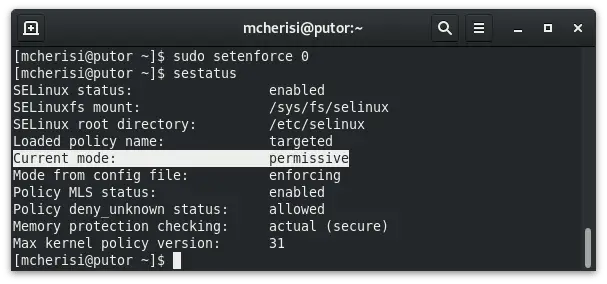
To temporarily set SELinux into permissive mode use the setenforce command followed by 0.
sudo setenforce 0This will set SELinux into permissive mode. In this mode SELinux will not block anything. However, it will still log actions that would have been blocked. This allows you to disable SELinux to test a service or other access denied errors. It also provides valuable information in the logs.
TIP: The default log for SELinux denials is /var/log/audit/audit.log
Here we can see that sestatus now reports the current mode as permissive.
You can use the following command to place SELinux back into enforcing mode (flip the bit back to 1).
sudo setenforce 1NOTE: Using setenforce to disable SELinux is temporary in the context that it will not survive a reboot. SELinux will start in the mode that is set in the configuration file when the system is boots.
Permanently Disable SELinux
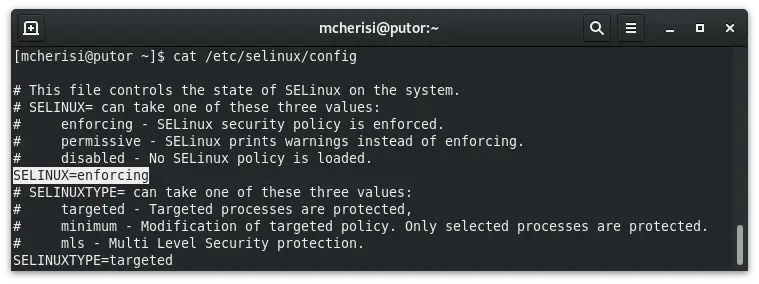
A reoccurring theme in Linux is that simple commands change can change the state of a service. But if you want it to survive a reboot (i.e. make it permanent), you must change a configuration file. This is no different with SELinux. If you want to permanently disable SELinux, you must change the /etc/selinux/config file.
Here is what the config file looks like with SELinux enabled. Notice the highlighted text.
To permanently disable SELinux you need to edit this file and change the highlighted line to:
SELINUX=disabledSince this is a kernel module, a reboot is required to load the new configuration.
NOTE: Putorius does NOT recommend disabling SELinux. It is a major part of your systems security. This should only be done for testing or troubleshooting purposes. Any changes to your systems are the system owners responsibility.
Conclusion
In this quick tip we showed you how to use getenforce and setenforce to view and change the current SELinux mode. We also discussed changing the configuration files to permanently disable SELiunx.
I would like to stress the importance of SELinux. In the past I have seen many people disable SELinux because they don’t truly understand how to work with it. I highly recommend that you take the time to understand SELinux, or at least the basics. Disabling it permanently greatly reduces your systems security posture.
If you would like to see more articles on SELinux, let us know in the comments. Or better yet, contribute an article.
Resources and Links
Join Our Newsletter
Categories
- Bash Scripting (17)
- Basic Commands (51)
- Featured (7)
- Just for Fun (5)
- Linux Quick Tips (98)
- Linux Tutorials (65)
- Miscellaneous (15)
- Network Tools (6)
- Reviews (2)
- Security (32)
- Smart Home (1)